Our survey conducted among 260 IT decision-makers shows a lack of risk awareness and no clear responsibility for IoT security
Bad Homburg, April 21st, 2021 — Smart devices – Although they are used in virtually all industries, the security risks associated with them are widely underestimated. 42% of 260 companies surveyed as part of the “IoT Security Report 2021” have not set any compliance rules for their IoT devices such as routers, Wi-Fi access points, VoIP telephones, network cameras or IoT devices in production (IIoT). “The results are startling. Although the majority of the companies surveyed see the Internet of Things as a security risk, only a minority of them safeguard their business by taking adequate measures,” commented Rainer M. Richter, managing director of the German company IoT Inspector. In April 2021, the survey was conducted at decision-maker level among German companies of different sizes. For example, 22% rely on contractual agreements with manufacturers when it comes to device security. Only 11% conduct a threat analysis, while 28 percent rely on penetration testing. Intrusion detection is carried out by only 37% of the companies surveyed.
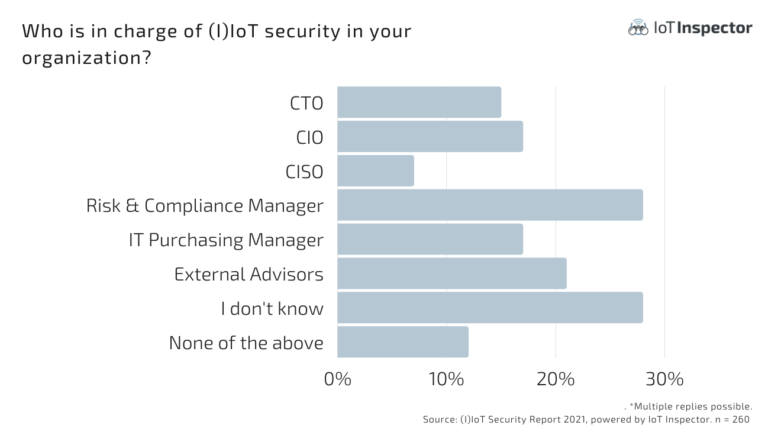
Who is in charge of (I)IoT security in your organization?
Unclear Responsibilities
Another critical issue is the vacuum that exists around the topic of responsibility concerning IoT security. At 15% of the 260 companies, the burden is on the CTO, and at 17%, the CIO. 17% have the responsibility resting with procurement, and another 21% rely on external consultants. “This is gross negligence! Any IoT device can be tampered with and poses a corresponding security risk to a company. The responsibility must lie with the same person or department in charge of the rest of IT security,” says Richter. His company operates a security platform for analyzing IoT firmware — the operating systems of such smart devices — for security vulnerabilities and compliance violations. Among the main problems are intransparent OEM supply chains, when products are sold by a manufacturer but not necessarily manufactured by them. Re-labeling often allows for undesirable security vulnerabilities to be smuggled into the final product. “It is quite possible that the original third-party provider still has full access to the device — and may use it to access a company’s network,” warns Rainer Richter. This has just been clearly demonstrated by the Dutch telecommunications provider KPN and its Huawei infrastructure.
KPN: Did Huawei Help with Espionage?
The controversial Chinese company Huawei manages equipment in KPN’s mobile network. According to Dutch sources, Huawei employees in China and the Netherlands may even have “administrator rights” in the KPN network, and thus also the opportunity to listen in on conversations up to the highest political level, or pass them on to intelligence agencies. “This example shows what kind of “bomb” can be found in supposedly harmless devices that are mindlessly integrated into an infrastructure and then forgotten about during operation,” says Richter from IoT Inspector. In the U.S., Huawei has already been on the banned list for use in government agencies since 2019.
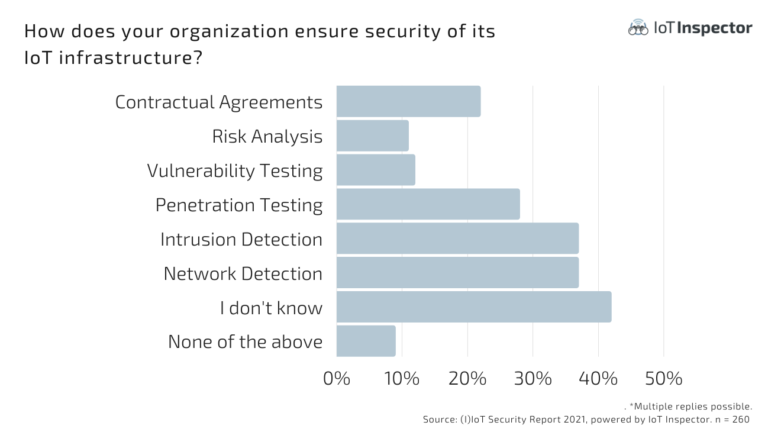
How does your organization ensure security of its IoT infrastructure?
But hackers also have it so easy, at least according to the 260 company representatives surveyed. 85% confirm that cybercriminals have already set their sights on IoT devices. The respondents see servers, PCs, and Industry 4.0 systems as particularly threatened. Medical devices with network connections, on the other hand, are considered at risk by only 28%, and IP phones by only 14%. “This is a gross misjudgment that may have been valid ten years ago. Today, every device — from routers and video conferencing systems to keyless entry systems — is a Trojan horse for attacks on companies and organizations,” warns IoT expert Richter.






